Veeam Backup & Replication Best Practices: #2 – Hypervisor, Backup Job and Restore

Table of Contents
StoneFly and Veeam Offer state of the Art backup and disaster recovery solutions for Commercial, Public Sector and Cloud Service Providers. Veeam is the premier availability software for StoneFly, which offers high performance, elastic and always available IT infrastructure solutions. This blog discusses the Veeam Backup & Replication V9.5 best practices for supported hypervisors, backup jobs as well as the restore options.
Recommended Operating Systems
When deploying Veeam servers, use the latest approved 64-bit Windows operating system for your environment. Veeam recommends using Windows Server 2016. Windows Server 2016 is fully supported for all Veeam Backup & Replication 9.5 operations. See Veeam Backup & Replication 9.5 documentation for more details. If you deploy Windows Server 2016 VMs, make sure your version of the hypervisor fully supports them.
VMware vSphere Support
Veeam Backup & Recovery 9.0 added Direct NFS as a new transport method for vSphere environments that use NFS datastores; Direct NFS supports both NFS 3.0 and 4.1. StoneFly and Veeam recommend that vSphere customers configure Veeam Backup & Replication to use the Direct NFS method, as it provides the highest possible performance and minimizes the physical network load. When using VMware vSphere, deploy a Veeam proxy VM on each server node. If you cannot use Direct NFS for some reason (such as the presence of an existing VM snapshot), Veeam Backup & Replication seamlessly falls back to network transport mode. However, network transport mode does not perform as well as Direct NFS, so backup windows may take longer.
When you can’t use Direct NFS, Veeam Backup & Replication fails back to network transport mode. Network transport mode connects to the ESXi management VMkernel port and transfers backup data to the proxy. It uses the VMware Network File Copy (NFC) protocol, which has a maximum throughput limit of around 40–50 percent of the VMkernel interface. In addition, with vSphere 6.5 and some versions of the VMware Virtual Disk Development Kit (VDDK), encryption of VMkernel traffic (NBD) may be required, though enabling NBD encryption can have up to a 30 percent negative performance impact. VDDK 6.5.0b removed the SSL requirement for NBD, making SSL optional. Beginning with version 9.5 update 3, Veeam Backup & Replication installs VDDK 6.5.0b—thus, by default, NBD traffic is not encrypted. For previous Veeam versions with vSphere 6.5, use Direct NFS as much as possible. Customers can force NBD over SSL (NBDSSL) if they need to (for example, when backing up encrypted VMs), but be aware of the potential performance impact.
For the best performance of network transport mode, the ESXi management VMkernel port must use the dual 10 GbE NIC interfaces. Managing the ESXi host through the 1 GbE NICs severely degrades backup performance. Rather than using the 1 GbE NICs, consider creating an additional VMkernel port over an available 10 GbE NIC interface, then configuring the Veeam preferred backup network to use this network.
VMware vSphere Best Practices
- Use Veeam Backup & Replication version 9.5 update 3 or later for all environments (required for EnableSameHostDirectNFSMode operation).
- Set EnableSameHostDirectNFSMode to 1 (Veeam Backup & Recovery 9.5 U3 and later).
- If using vSphere 6.0, use at least ESXi 6.0 Build 5572656 (6.0 patch 5) to avoid serious Change Block Tracking (CBT) bugs. We recommend using the latest patch wherever possible. See VMware KB 2143832 for ESXi build numbers.
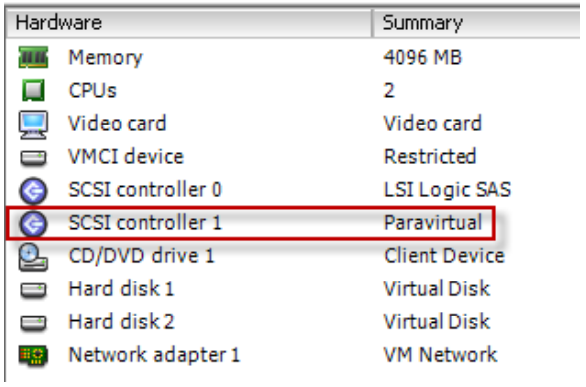
- If you are using a virtualized repository server, configure a second SCSI controller to use with the VMware PVSCSI controller. Add the repository disks to this second controller.
- Use the latest VM hardware version for Veeam Backup & Replication VMs.
- Always use the VMXNET3 NIC for Veeam Backup & Replication VMs.
- If you are using the VMware Distributed Switch (recommended), use LBT load balancing.
- Right-size the proxy VM according to Veeam best practices for your environment.
- Use Direct NFS. Do not use network transport mode unless the environment is very small with small VM change rates.
- Do not use virtual appliance backup mode.
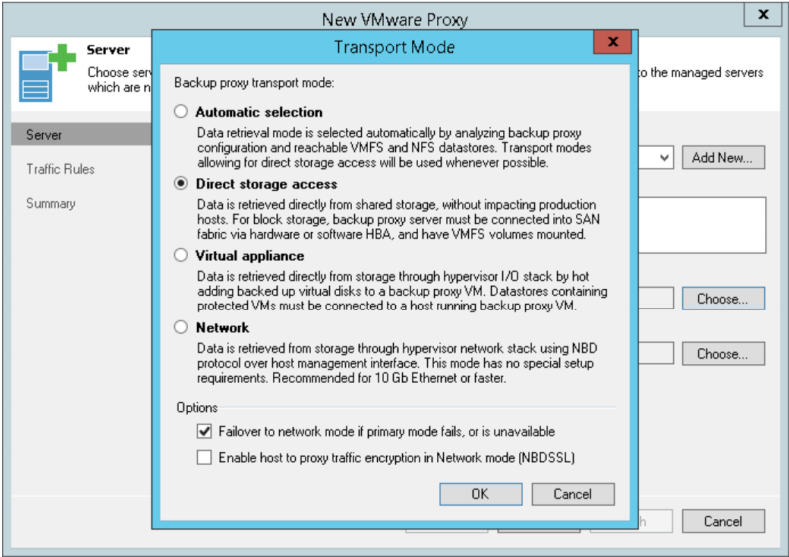
- When configuring the Veeam VMware proxy, select Direct storage access and enable Failover to network mode if primary mode fails, as shown in the screenshot below.
- Review Veeam logs to confirm that backup jobs really are using Direct NFS.
Microsoft Hyper-V Support
In contrast to the vSphere deployment model, using Veeam Backup & Replication with Hyper-V does not require per-node proxy VMs. Instead, Veeam installs a lightweight proxy component into each Hyper-V parent partition as it is added to the Veeam Backup Server.
As with VMware environments, it’s critical for performance that the Hyper-V management interface use the dual 10 GbE NICs. Introducing routing or other network devices, such as a firewall, between the proxy agents and the repository can negatively impact performance. Microsoft Hyper-V 2016 has built-in resilient change tracking (RCT). Using this feature, Veeam Backup & Replication V9.5 can greatly reduce backup windows after completing the first full backup job.
Microsoft Hyper-V Best Practices
- For Hyper-V 2012 R2, deselect the CBT option for all jobs.
- For Hyper-V 2016, use RCT on all jobs.
- Configure backup jobs to use on-host backup as the proxy.
- For optimal backup performance (namely, RCT), migrate to Hyper-V 2016.
Veeam Backup Job Best Practices
StoneFly and Veeam recommend using the forward incremental method with synthetic full backups. This method is the default setting for jobs newly created in Veeam Backup & Replication V9.5; you can also select it for existing jobs if you are upgrading from previous versions. When using this method, Veeam performs a full backup on day one, then creates incremental backups for all subsequent days. On a weekly basis, the solution synthetically combines the available daily incremental backups with the original full backup to create a new full backup, without the need to retrieve all the data from production storage. The day-one backup may have lower throughput, because it reads all VM data, which may be in the capacity tier as well as in the performance SSD tier. However, for hypervisors supporting a CBT mechanism, all subsequent backups only read changed blocks.
To enable parallel processing and increase backup performance, configure your jobs to back up multiple VMs. Also, when you increase the number of VMs inside the same job, Veeam-native deduplication can be more efficient. There is no need to manually configure which proxy VM the backup operations use; Veeam Backup Server automatically distributes the VMs scheduled for processing to all available proxies.
Veeam Restore Options
Veeam Backup & Replication solution offers a range of options to easily recover and verify your replicas and backups. These features are implemented using the Veeam vPower technology. Veeam vPower allows instant recovery of a VM in Hyper-V and VMware environments. Instead of waiting for the VM to restore from backups, instant-VM-recovery allows you to run the VM directly from the backup. vPower technology performs the following tasks:
- Instant-VM-recovery.
- Recovery verification (SureBackup, SureReplica).
- Universal Application-Item Recovery (U-AIR).
- Multiple-OS file-level recovery.
Veeam Backup & Replication appliance allows you to perform both file-level and image-level restores of replicas and backups. You can restore an entire VM and start it on the target server, or recover only VM hard disks, VM files (.vmx, .vmdk, .vhdx, and so on), or VM guest OS folders and files and save them on your local machine. You can restore files or VMs at any of the available restore points. All restores occur via the network, and you do not need special procedures to restore your data.