S3 object lockdown is a ransomware-proof data protection feature. With StoneFly’s patented storage virtualization engine, our customers can choose to set up S3 object lockdown on-premises, in the cloud, and on virtualization environment(s) such as VMware, Hyper-V, KVM, or Citrix (formerly XenServer).
In this blog post, we’ll cover what S3 object lockdown is, why you need to include S3 object lockdown in your cybersecurity strategy, and how to do so.
What is S3 Object Lockdown?
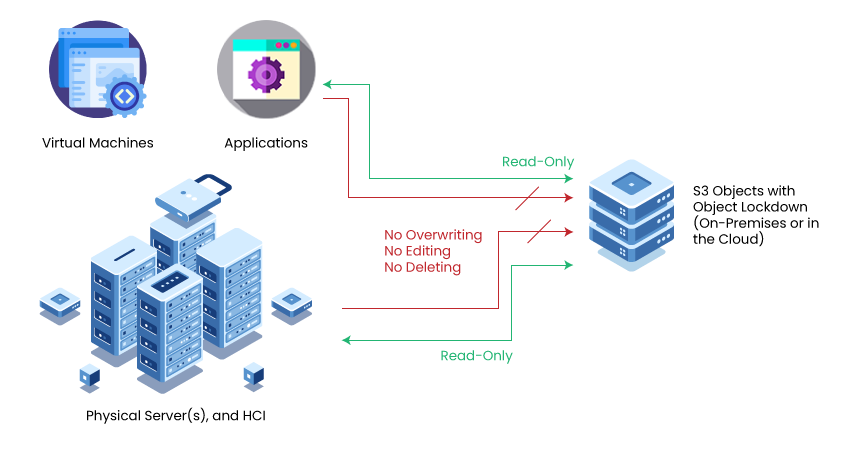
S3 object lockdown is an immutability feature – it allows IT administrators to “lock” target storage volumes for a specified period of time. When locked, the data stored in these volumes cannot be edited, overwritten, or deleted.
IT administrators can choose to set storage immutability for a period of time or indefinitely – depending on their requirement(s).
As these volumes cannot be edited, this also makes the data stored in them safe from ransomware attacks, and disasters such as human error, accidental/malicious deletion, and virus.
The fact that the immutable storage volumes protect data from cyber-threats, they make compliance easier and are good target storage for critical data such as backups, snapshots, and replicas.
Why Do You Need S3 Object Storage Lockdown
Here are two reasons why you need to make S3 object storage lockdown part of your cybersecurity strategy:
Ransomware Protection for Your S3 Object Workloads
Over the past year, ransomware attacks increased by 93% – and this number is expected to grow even further.
With object lockdown, IT administrators can protect business-critical workloads, customer data, backups and snapshots. In the event of a ransomware attack, as the data stored in locked object volumes is immutable, it is protected from malicious encryption.
Once the production environment, and backup server(s), are recovered and ransomware is removed, the data stored in these volumes can be used to restore critical operations.
Note: The object lockdown feature does not prevent a ransomware attack from infecting your system(s) and network. It makes data immutable – preventing ransomware from affecting it.
Compliance with HIPAA/HITRUST, FedRAMP, CJIS, and More
In addition to protecting data from unauthorized access, immutable storage also facilitate regulations that require businesses to retain confidential information.
Here are some examples of organization(s) that can use S3 object lockdown:
- Healthcare service providers need to retain patient information and medical records for 10 years or more.
- Financial companies, such as banks and insurance companies, have to maintain account information and transaction records for 5 years or more.
- Educational institutes, such as schools; colleges; universities; retain research papers, student information, and scholarship and grant program details for longer periods of time.
- Law enforcement agencies process and collect terabytes of security camera footage and dashboard cameras. This footage is often times crucial to criminal proceedings and needs to be retained for several years.
S3 Object Lockdown versus Air-Gapping
While many experts would have you believe that the S3 object lockdown is the same as air-gapping. Although, the purpose of both object lockdown and air-gapping is the same, the way it’s done is fundamentally different.
S3 object lockdown protects data from being overwritten or deleted while allowing users to read it. Air-gapping on the other hand completely isolates data from the network – preventing applications and users from accessing it.
In other words, S3 object lockdown shouldn’t replace air-gapping or used as an alternative, both should be used in tandem in a cybersecurity strategy.
How to prepare your environment for S3 object lockdown
Looking to add S3 object lockdown to your environment? Here’s a brief checklist to help walk you through the process and make the integration streamlined:
Evaluate Your Requirements: Is your business subject to compliance regulation(s)? Do you need to set up retention period(s) and legal hold(s)? If so, for how long? Analyze the data lifecycle of your workloads so that you can leverage S3 object lockdown effectively in order to meet compliance requirement(s) and customer expectation(s).
Consider Hybrid Implementation: With a hybrid environment, you can set up immutable volumes on-premises and in the cloud. This enables you to make the most of your available resources while minimizing the cost of storage. Furthermore, hybrid environment(s) also facilitate the implementation of backup strategies such as 3-2-1, 3-2-1-1-0, and 4-3-2.
Test and Monitor: It goes without saying that the solution you choose should accommodate all of your requirement(s). Be sure to test out the functionality of the chosen solution before you decide to integrate it with your existing environment(s). It’s also important to continue to monitor usage to make sure that the integrated immutable storage is used as intended and there’s little room for human error.
How to Add S3 Object Lockdown to Your Existing Environment(s)
If you’re looking to integrate S3 object lockdown with your existing environment(s), StoneFly offers multiple customizable options:
Add S3 Object Lockdown to Your Virtual Environment(s):
Install StoneFly SCVM™ on your virtual environment and set up S3 object lockdown on-premises and/or in the cloud.
StoneFly SCVM is an 8th generation storage virtualization engine compatible with most mainstream hypervisors including VMware, Microsoft Hyper-V, KVM, and Citrix (formerly XenServer).
SCVM allows you to reclaim unused and idle storage space to provision S3 objects, which can be locked as needed.
With SCVM configured as a cloud gateway, you can choose to integrate public clouds such as Microsoft Azure, Amazon Web Services (AWS), and/or StoneFly private cloud – and configure object lockdown in the cloud.
Integrate Cloud-Based S3 Object Lockdown
Connect your IT system(s), server(s), and virtual environment(s) to cloud storage with S3 object lockdown using StoneFly Smart cloud gateway and StoneFly storage service(s) in Azure, AWS, and StoneFly private cloud.
The Smart cloud gateway is available as a hardware appliance and virtual appliance.
Purpose-built S3 Appliances with Built-in S3 Object Lockdown
Get a purpose-built cloud-native S3-compatible storage appliance with built-in S3 object lockdown feature from StoneFly.
The S3 storage appliance support mainstream virtualization environment(s) such as VMware, Hyper-V, KVM, and Citrix (formerly XenServer), and cloud(s) such as Microsoft Azure, AWS services, and any other S3 compatible cloud(s).
Conclusion
With ransomware attacks targeting small-to-medium businesses (SMBs), healthcare service providers, financial service providers, and large enterprises, cybersecurity solutions have become a necessity for data owners and data processors of all scale.
One of the best ways to protect your S3 object workloads is by using S3 object lockdown feature.
S3 object lockdown enables IT administrators to restrict access permissions to allow read-only. The data stored in these “locked” volumes cannot be overwritten, edited, or deleted for a user-specified period of time.
StoneFly offers customizable cloud, virtual, and hardware solutions with S3 object lockdown compatible with mainstream virtualization environment(s), cloud(s), application(s), and physical server(s).
Looking to integrate S3 object lockdown with your data center? Contact our representative using the live chat feature, email [email protected], or call us at +1 510 265-1616.