The global IT industry is moving to the cloud at an amazing rate. Each cloud backup service provider comes up with unique solutions to various problems. Every enterprise has unique data requirements, it isn’t necessary that a certain solution would comply with every problem.
Similarly, every service provider isn’t necessarily capable of addressing an enterprise’s requirements. The usual marketing strategies work in such a way that once you acquire a solution from a vendor, you’re caught in a lock-in situation. In accordance to the usual marketing strategies, the acquisition of a single solution constitutes a lock-in. There’s a reason why Amazon Web Services (AWS) alone continues to grow over 40% each year while Microsoft boasts a revenue rate of around $15 billion by including Office 365 SaaS (Software as a Service) offerings.
What is meant by lock-in?
A decade ago, AWS pioneered its Standard Storage Service (S3). The approach was to provide storage services at cut rate and to facilitate data to enter their servers; however, the system was designed to ensure that this data would never leave.
Amazon offers a range of storage solutions to address different types of data: S3, S3-IA, Reduced Redundant Storage, Glacier and more. The users can migrate their data from one storage tier to another using Amazon tools. However, if you wish to opt out of Amazon and secure some other cloud service then there is no Amazon tool or service that helps you to do so. You simply cannot move your data from Amazon S3 to Microsoft Azure Cool blob storage; it has to move from S3 to S3-IA. This is what’s referred to as a lock-in.
This isn’t limited to Amazon; Microsoft is doing the same thing. If you acquire Azure Hot blob storage, then you cannot migrate your data to S3-IA; it has to be moved to Azure Cool blob Storage.
Inconveniences caused by vendor Lock-in
The harm in this lock-in is that it’s a major hurdle in the construction of a comprehensive backup and disaster recovery plan.
For instance, consider Amazon Macie. It is an AI (Artificial Intelligence) that employs machine learning to classify data based on sensitivity and secures it by observing user behavior patterns. This is a convenient service that will ensure that your data isn’t incorrectly configured or your sensitive data isn’t publicly accessible. Despite its convenient features, it is not available to Microsoft Azure users directly.
Similarly, now consider Azure Confidential Computing. This is a storage service that resembles a black box. You can store your data in it and even Microsoft cannot access it. Azure Confidential Computing redefines security protocols, makes data immutable and inaccessible. Even governments, cannot acquire the data stored in this storage space, And Azure clients cannot gain access to this service directly.
Simply put, regardless of which vendor you choose you are compromising on one or more convenient service that can heavily support your DR (disaster recovery) plan.
StoneFly’s Cloud Gateway Appliances Facilitating Multi-cloud Solutions
StoneFly provides a number of backup appliances and cloud gateway appliances that can access public clouds and StoneFly’s private cloud. Using these solutions, you can acquire services from both Amazon and Microsoft. By using multiple gateway appliances, you can configure your existing infrastructure to utilize services that are convenient for your backup and DR plan.
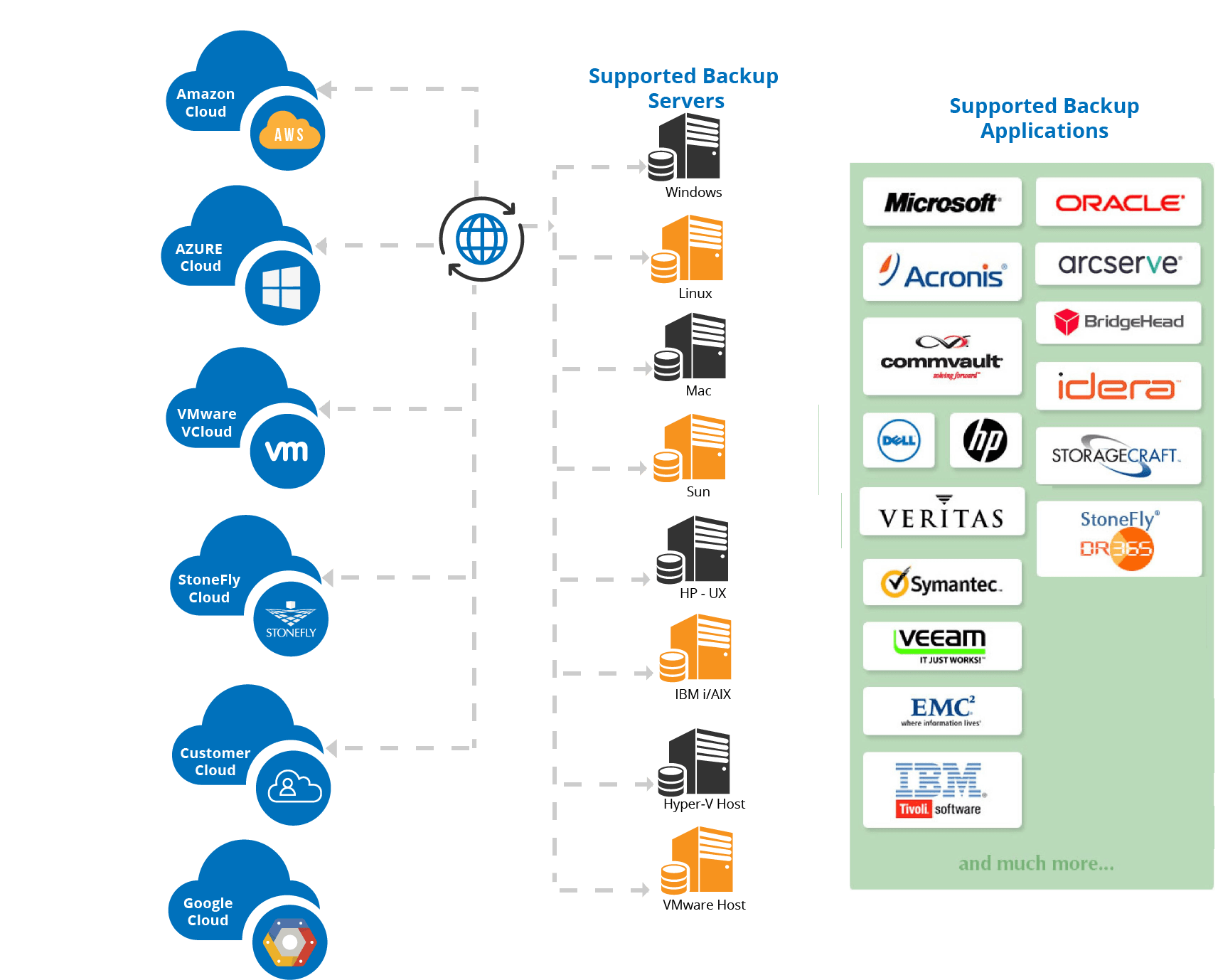
StoneFly is compatible with a number of clouds, backup servers and languages.
If you have existing backup infrastructure, it can acquire multi-cloud services by using multiple cloud gateway appliances. And if you don’t have backup infrastructure, then you can acquire StoneFly’s appliances and establish an infrastructure that is flexible, highly compatible and facilitates backup to AWS and Microsoft Azure.
You can create backups on your local infrastructure, then create copies on public clouds while using StoneFly’s private cloud for replication services.
Conclusion
Enterprises have unique data backup requirements. These requirements simply cannot remain within the boundaries of a single vendor’s services. However, mainstream cloud service providers constitute a lock-in. This lock-in can be a major hurdle for comprehensive enterprise cloud storage and backup solutions. StoneFly cloud connect gateway solutions enable you to acquire multi-cloud services. So you can employ solutions that are best suited to your requirements instead of adapting to the list of solutions available to you.