2021 is the year of automation, machine learning, artificial intelligence and compliance regulations. GDPR is only months away and service providers and service users alike are reaching out to compliant solutions, so they don’t have to deal with the consequences. In light of this, public cloud service providers like Amazon Web Services and Microsoft Azure Cloud are investing in compliant services and features.
This brings us to the latest release of Microsoft: automation for HIPAA/HITRUST compliance. The solution is made to take a sample data set formatted using Fast Healthcare Interoperability Resources (FHIR) and store it in a secure manner. End users can then use Azure Machine learning to use business intelligence tools for analytics and forecasting using the stored sample data. Before we discuss the automation, let’s review HIPAA/HITRUST compliance regulations first.
What is HIPAA and HITRUST compliance?
HIPAA (Health Insurance Portability and Accountability Act) defines rules and regulations for companies that deal with patient data. These rules require companies to make sure that all of the Protected Health Information (PHI) being processed by their computers, network, physical and virtual appliances is well protected from unwarranted access and data leakage. This is a rather brief definition of the regulation but the implications cover business associates, covered entities, sub-contractors and basically everyone who accesses, stores and maintains health information. HITRUST or Health Information Trust Alliance is a certifiable framework that synchronizes various other compliance frameworks such as HIPAA, PCI, ISO, NIST etc. HITRUST is simply, an attempt to aid vendors of the healthcare industry to prove their security protocols and to help covered entities to streamline security and compliance reviews.
Microsoft Azure’s Automation for HIPAA/HITRUST Compliance
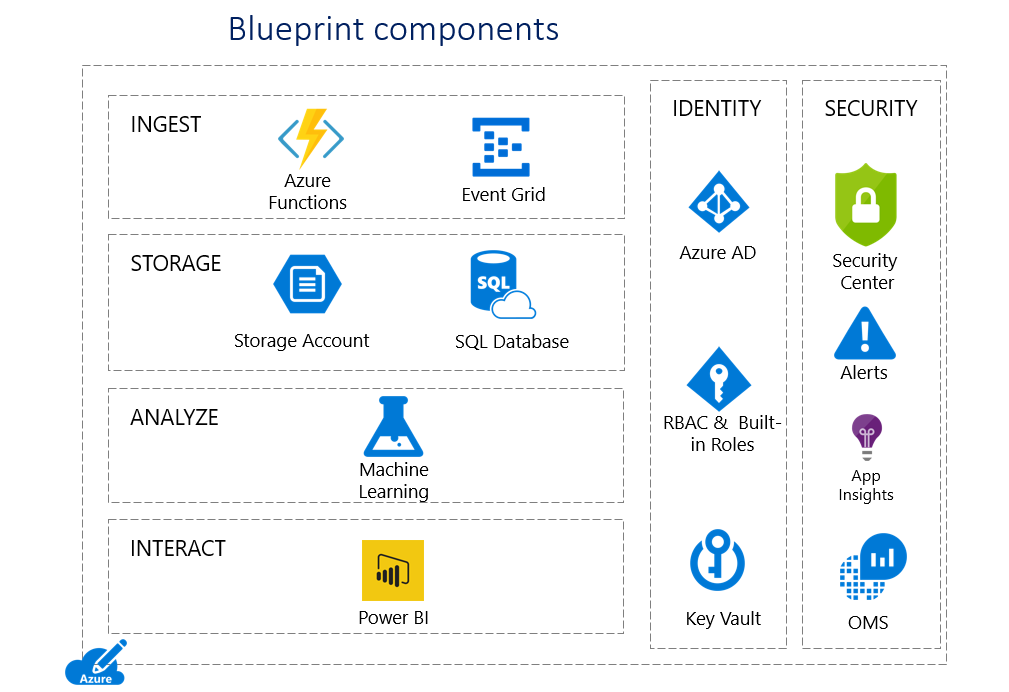
Microsoft Azure Cloud Storage has been compliant to HIPAA/HITRUST and other regulations like FedRAMP since ages. This solution, as the name suggests, helps automate the storage process that remains compliant with the industry regulations. In order to simplify the usage of this solution, Microsoft has also provided a blueprint. The blueprint contains resources that help in building and launching the cloud powered application that will be HIPAA and HITRUST compliant. The blueprint also includes reference architectures, compliance guidance and deployment scripts.
This blueprint is intended to explain how to deploy secure end-to-end health solutions that include PHI, and:
- Machine learning experiment to forecast the length of stay of patients.
- Sample data set of 100,000 patient records.
- Azure Resource Manager Templates and PowerShell automation scripts.
- Threat model for use with Microsoft Threat Modeling Tool.
- A Microsoft Excel Workbook containing applicable HIPAA/HITRUST requirements.
- A report by Coalfire Systems with an auditor’s review of the solution.
A thing to note here is that despite being a complicate enterprise cloud storage, using Azure cloud doesn’t make you compliant until you conduct an appropriate security and compliance review of all solutions dealing with PHI. Microsoft released a video explaining and demonstrating the deployment process.
Deploy StoneFly and Microsoft Azure Cloud’s Compliant Solution
StoneFly’s partnership with Microsoft Azure allows StoneFly’s appliances to use cloud connect services and utilize Microsoft Azure cloud’s compliant storage. StoneFly also offers cloud gateway appliances that can empower legacy infrastructure by integrating Azure cloud or AWS cloud and facilitate backup to AWS or Azure. Our innovative technology can efficiently address all kinds of enterprise backup requirements. Schedule a demo, discuss your data requirements and let our solution experts come up with a customized solution befitting your requirements.