Difference Between Disaster Recovery as a Service (DRaaS) and Cloud Backup

Table of Contents
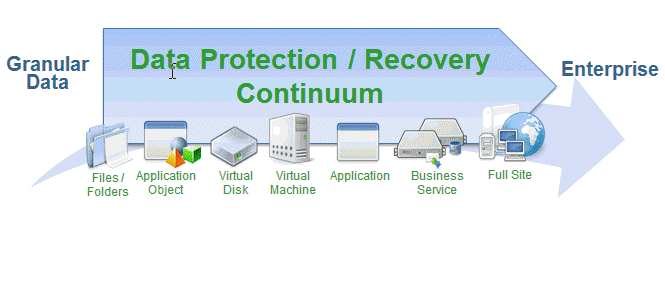
Backup and Recovery are critical components of Disaster Recovery, but if they work alone, they cannot assure that application processing continues uninterrupted.
One of the great advantages of cloud-based failover is that small companies can now afford contract for a cloud-based failover. It is more expensive than just using cloud-based backup and recovery but also on the other end it is less costly than building secondary data centers, and we call this service as a Disaster Recovery as a Service (DRaaS).
The two primary services for the cloud-based data protection include Backup as a service (BaaS) and disaster recovery as a service (DRaaS). They are defined as:
It is a cloud-based backup to the service provider. The service provider is responsible for backing up contracted data and meeting recovery service levels. Following the disaster, IT rebuilds the server environment, install applications and then restores the data from the cloud.
Backups have multiple checkpoints going back in time (up to a year) depending on your retention policy. The recovery time is always going to be based on the size of the machine or of the data. But you can bring a single file or a single Virtual Machine (VM) backup for any checkpoint (in time) into the primary site where the machines were already running.
- Recovery as a Service (RaaS)
It is basically one step further of BaaS as it restores applications as well as data from the cloud. It works by hosting server images and production data backup in the host’s data center. Upon a recovery request, the provider downloads images and data to the customer site.
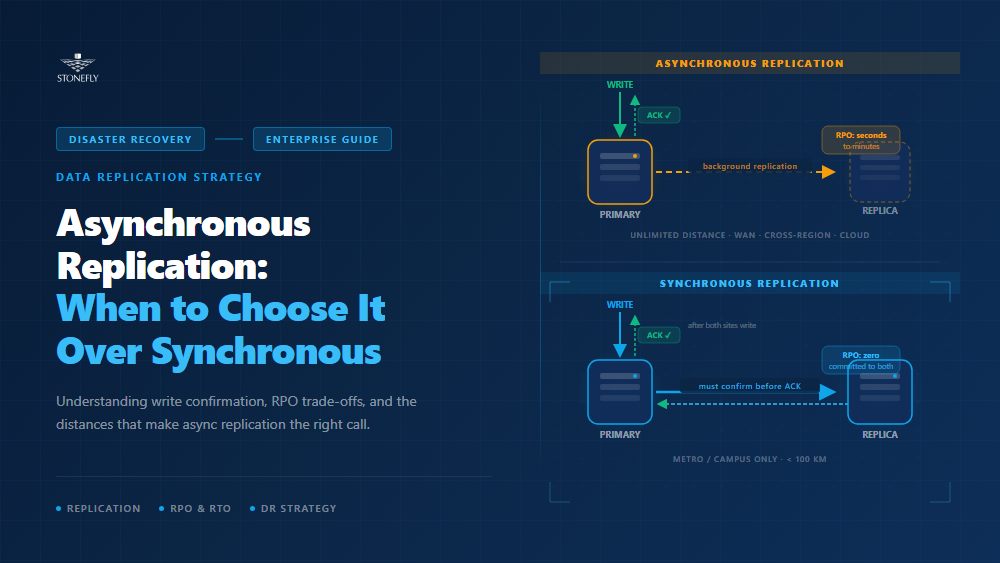
DRaaS adds cloud-based failover to backup and recovery services. Failover maybe based on public cloud or Service provider’s Private cloud, and it may be automated or manual. DRaaS includes backup and recovery services. This service is more extensive than RaaS and more expensive, but if you have critical applications then it is worth it.
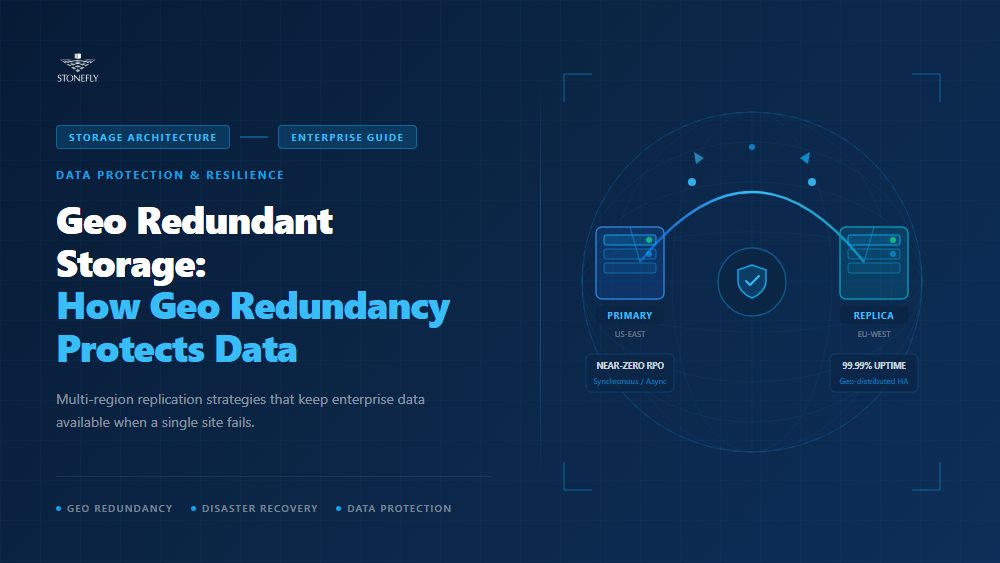
Disaster Recovery is a service that focuses entirely on a short RPO, meaning that the data we are restoring from is close to Present time as possible. It’s going to bring the machine up in a geographically different source protected from whatever has happened to your data in the original site.
DRaaS is not by definition necessarily based in the cloud. Some service providers offer DRaaS as a site-to-site service where they host and operate a secondary hot site. Others provide server replacement, where they rebuild and ship servers to the client site.
The Primary advantage of DRaaS is its immediate failover applications reconnect users via VPN and orchestrate failback to rebuilt servers in the customer data center.
Cloud-based disaster recovery service providers deliver their services in different ways. Some use appliances; some limit failover to the cloud while others offer managed site-to-site failover as well.
The thing to think about with the two is both your time and where the data is restored from. If you are running a business you need to think about your resiliency strategy of both having archival data and the ability to protect it from downtime with disaster recovery as a service. They both work together to protect the business and to protect the revenue flow.