Business Continuity & Disaster Recovery: What’s the difference?

Table of Contents
Often times, business continuity and Disaster Recovery (DR) are used inter-changeably. The two strategies are related but not exactly the same. In this article, we differentiate business continuity from disaster recovery and discuss how StoneFly DR solutions can play an integral part in enterprise business continuity.
What is Business Continuity?
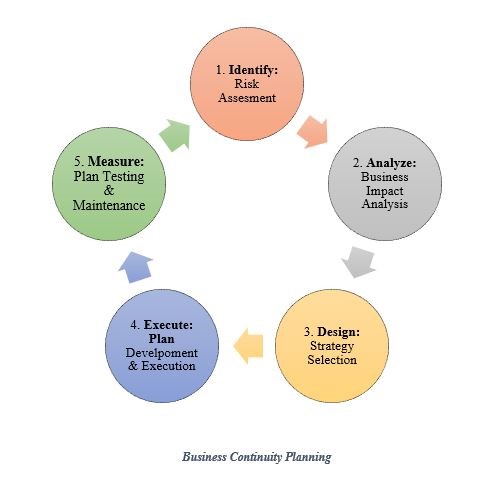
When you look at business continuity, it is an ongoing process, it’s not a one-time event rather it’s an overview of the lifecycle of your business. It’s like; how do I protect or how do I assess the risk? How do I analyze what I’m going to need? Then you need to design it and it has to incorporate all aspects of your business.
It’s not just IT, if you’re a retail store, for example, it’s looking at your stores, your manufacturing facilities, your warehouses, your IT, your administrative staff and your people. So it’s very important that you consider the whole process.

Business Continuity Planning
In business continuity, another interesting concept is that who is responsible for business continuity planning? For years you would see that IT would handle both business continuity planning and disaster recovery, and in some of the bigger organizations, over the years, it has been observed that business continuity planning was moved into the business where it should be.
With this in mind it is important to know that disaster recovery planning is part of a larger BCP process. It’s an integral part and it supports most of the business applications that are out there because they are oftentimes automated. But it’s not the only part and it should be one thing that the business is looking at when they’re trying to determine how to protect their business and how to stay in business.
What does Disaster Recovery Mean?

Disaster recovery is mainly focused on the protection of IT assets. It could be facilities, it could be hardware, it can be software and it could be people. The people’s one is oftentimes a forgotten attribute. It’s one that people don’t put enough weight into.
Disaster recovery with regards to people needs consideration of where they live, where they have to go to, their emergency contacts and how to respond to a disaster event. In this blog, we are going to focus at disaster recovery of IT assets.
A good example of this is the recovery story of one of our customers, we recently talked to the CTO of a bank. He shared his story of a disaster that they recently faced. What they encountered was a major hardware failure for their primary systems. Their customers could not make any transactions, admin staff also lost access to their systems and this meant that everything came to a screeching halt and it created a lot of panic.
This happened before they had a DR system. Once they got a replacement and set up a DR system, they had no such issues. Now whenever a server within their nodes fails, they can easily recover it within 15 minutes because their DR system has replicas and since the system is on-premises, the recovery does not take a lot of time.
This means that all their mission-critical systems were back up and running with minimal downtime.
DRP in Contingency Management
Another way of looking at this is that disaster recovery planning is just a piece, but a significant piece, of contingency management. You’re looking at assigning the risk, you’re looking at media plans, you’re looking at validating and testing the entire business continuity plan not just the DR side of it.
So it truly is a bigger view. It’s a view of the business and DR, should be you know one piece of it. There are different schools of thoughts and of course with different size organizations it could vary on where the resources are available but business continuity itself should be run by the business and of course, disaster recovery should be a piece of business continuity.
How can StoneFly Help?
StoneFly can take care of disaster recovery or protection of IT assets. Stonefly offers several backup and disaster recovery solutions that are reliable, effective and cost efficient. These solutions are suitable for Small and Medium sized Businesses (SMBs) and large organizations. No matter the size of your business, StoneFly has backup and disaster recovery solutions for all.
Mainly, StoneFly offers two main types of backup and DR solutions:
- Disaster Recovery Appliance- Physical Appliance or Hardware Chassis
- Cloud Based Disaster Recovery
Disaster Recovery Appliances
StoneFly offers reliable and cost efficient backup and disaster recovery appliances with a variety of customizable options.
In business continuity and disaster recovery what really matters is how fast you recover from a disaster event. StoneFly 8th generation backup and DR appliances specifically are built for this purpose. Our appliances offer features like; synchronous & asynchronous replication, delta-based snapshots, block-level data deduplication and many more.
To get a full list of features contact StoneFly pre-sales engineers.
Following is a list of backup and disaster recovery appliances that we offer:
- DR365- Backup & DR Appliance (DR Site in a Box)
- DR365V- Veeam Ready Backup & Disaster Recovery Appliance
- DR365U- Universal Backup & Disaster Recovery Appliance
- DR365Z- Purpose Built Zerto Backup Appliance
To learn more about our backup and DR appliances, click here.
Cloud Based Disaster Recovery
StoneFly’s CDR365 is a cloud based disaster recovery solution. It is a user-friendly tool that enables users to backup Windows desktop computer and servers, MS SQL servers, Microsoft Exchange, Linux Servers and macOS to the cloud storage of any choice.
CDR365 offers many state of the art backup and DR features such as block level backup, image and bare metal backup, ransomware protection and much more. Apart from this, CDR365 offers ease in managing backups and restoring them thanks to a centralized management console.
To learn more about CDR365, click here.
Conclusion
Business continuity and disaster recovery, although different, are inter related. Both are essential for a business in order for it to survive a disaster or data loss and remain functional. It is necessary for businesses to employ both strategies concurrently to compete in the digitally transformed market of today.
Set up a Reliable DR with StoneFly Solutions, Contact Us Today!
Email: [email protected]
Phone: +1 510 265 1616
Website: www.stonefly.com | www.iscsi.com
Connect with Us on Our Social Media Channels
Twitter: @stoneflyinc
Facebook: facebook.com/stoneflyinc
Youtube: youtube.com/stoneflyinc
Linkedin: linkedin.com/company/stonefly-networks