Five Stages of Security for Incident Response

Table of Contents
How many of you have a really strong security program where you have security incident response and things like that going? How many of you are still using the help desk to let you know when Ransomware hits?
A story of a C level Executive
Here is a story of a C level executive that was there for a manufacturing company who was running a live application in the cloud. Ransomware ended up hitting that server because he was browsing on sites through a server. As this happened, what we saw was that Ransomware has gotten so much smarter, that it started communicating back with him. The Ransomware attack that happened in the environment said;
“By the way we know that you have all of these financial files that are sitting on this server, and that you are testing with, and we know that you just replicated this and this is just a test environment. However, it still has this financial data that is relevant to your organization. And by the way, we looked up your organization and we see that you have 20,000 users”.
What are your Five Stages of Going through that Process?
Ransomware is starting to become more and more prominent where it is starting to communicate back with you and they are negotiating with you now. Cyber criminals are starting to become more and more prevalent as they start to attack your systems, whether it’s on-premise or in the cloud. But this was a threat that just happened in the cloud. So, what are your five stages of going through such process?
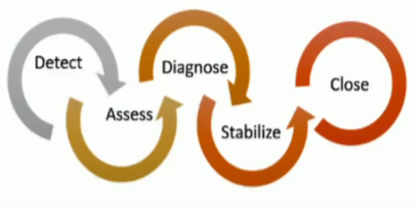
Detection
The first one is Detection, you need to go through a detection process. It is how you know it actually happened to you and where it happened.
Assessment
When you start to look at the impact and the severity of the event. what is your impact and urgency? How bad is it? How many people are you impacting and then what is your urgency? Can they work? Can they work with work arounds? Are they not able to work at all? Is it completely locking their system down?
Those two things help you calculate a priority based off your assessment.
Diagnosis
Based off of what you have gotten. That is where you start to diagnose what exactly happened. How does that process work, start to notify people, this is what’s happened, we have been breached.
Many people think that they have a really, really strong perimeter or they just have a really, really strong environment, they won’t be breached. Think again, most cloud attackers will find different penetration ways to go and hit you, the same way that OMS is going to assess your environment.
Stabilize and Recover
Once you have been hit or once you have a diagnosis of what incident has come through, that is where you can stabilize and recover. Stabilize and recover has the ability to do automation. So, find your top attacks that are hitting your organization, or find your top items that are inside of your organization already that you’ve just discovered as attacks with OMS and start to automate them or start to build PowerShell automations that then plug in to a security response
Close / Post mortem
And then finally, the last stage is to do a close and a post mortem on the incident event.
Want new articles before they get published?
Subscribe to our Awesome Newsletter.